INTERNET
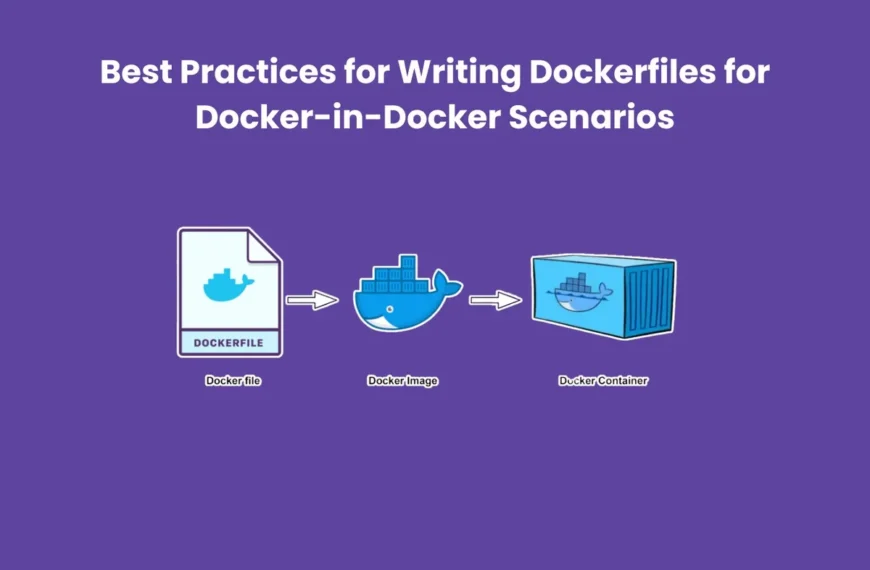
Best Practices for Writing Dockerfiles for Docker-in-Docker Scenarios
Table of Contents[Open][Close]Understanding Docker-in-Docker Dockerfiles Best PracticesUse a Base Image with Docker InstalledInstall Required Dependencies Early Minimise Layer CountLeverage Caching WiselySecure Docker-in-Docker ExecutionHandle Docker Socket AppropriatelyInclude Cleanup StepsOptimise for Build and RuntimeDocument…
Exploring the Power of Terminal Emulators: Unveiling Efficiency in Command Line Interfaces
Table of Contents[Open][Close]Bridging the Gap Between Mobile and Traditional ComputingUnveiling Efficiency and CustomizationSecurity and Learning Opportunities Terminal EmulatorsConclusion Terminal Emulators:In the realm of computing, the command line interface (CLI) has…
Unveiling iCloud Keychain: Your Shielded Vault in the Digital Realm
In the labyrinth of our digital lives, safeguarding sensitive information often feels like an intricate puzzle. Enter iCloud Identity Safe, an ingenious solution from Apple crafted to solve the password…
Understanding Intrusion Detection and Prevention Systems (IDPS): Safeguarding Networks Against Threats
Table of Contents[Open][Close]What are IDPS?Types of Intrusion Detection and Prevention Systems IDPS1. Network-Based (NIDPS):2. Host-Based (HIDPS):3. Wireless IDPS (WIDPS):Key Functions of IDPS1. Detection:2. Prevention:3. Logging and Reporting:Benefits of IDPS1. Proactive…
Unlocking Efficiency and Security with Identity Governance and Administration (IGA)
In today’s digital landscape, where data breaches and unauthorized access pose significant threats, organizations are navigating complex challenges to secure their sensitive information. Identity Governance and Administration (IGA) emerges as…
Streamlining Security: A Comprehensive Guide to VPN Setup and Management
Table of Contents[Open][Close]What is a VPN? VPN Setup and ManagementSetting Up Your VPNManaging Your VPNConclusion VPN Setup and Management: In an age where online security is a primary concern, Virtual…
Exploring Termux for PC: A Comprehensive Guide to Mobile-Style Computing on Your Desktop
Table of Contents[Open][Close]What is Termux for PC?Installing Termux on PCFeatures and Benefits of Termux for PCUse CasesConclusion In the world of mobile-style computing on desktop systems, Termux for PC has…
Enhancing IoT Network Security: Safeguarding the Future
Table of Contents[Open][Close]Understanding IoT Network SecurityEnhancing IoT Network SecurityConclusion The Internet of Things (IoT) has revolutionized the way we interact with technology, connecting everything from smart thermostats to industrial machinery.…
Unlocking Your Coding Potential with Termux for Programming
Table of Contents[Open][Close]Why Opt for Termux for Programming?The Versatility of Your SmartphoneA Plethora of Programming ResourcesText Editors Tailored to Your NeedsGetting Started with TermuxInstallationPackage ManagementEnhancing Your Development WorkflowVersion Control at…
Safeguarding Healthcare: The Vital Role of Cybersecurity in the Healthcare Industry
Table of Contents[Open][Close]Patient Data ProtectionPrevention of CyberattacksRegulatory Compliance Cybersecurity in the Healthcare IndustryMedical Device SecurityConclusion The healthcare industry stands at the forefront of technological innovation and medical advancements, enabling the…
How to Protect Personal Information Online from Hackers
Table of Contents[Open][Close]Understanding the Hacker’s MindThe Importance of Strong PasswordsTwo-Factor Authentication (2FA)Recognizing Phishing AttemptsSecure Browsing and HTTPSKeeping Software Up to DateSocial Media Privacy Settings Protect Personal InformationUsing Virtual Private Networks…
Best Cybersecurity Practices for Small Businesses
Table of Contents[Open][Close]Assess Your VulnerabilitiesConduct Regular Security AuditsEmployee Training Best Cybersecurity Practices for Small BusinessesProtect Your Network Install a FirewallUse Strong PasswordsData ProtectionEncrypt Your DataRegular BackupsImplement Security SoftwareAntivirus SoftwareEndpoint SecurityIncident…