Table of Contents
Digital Security Controls
In the age of digital transformation, where technology pervades every aspect of our lives, the importance of cybersecurity cannot be overstated. The ever-increasing threat landscape demands robust measures to safeguard sensitive data and protect against malicious cyber attacks. Digital security controls play a pivotal role in enhancing cybersecurity, providing a comprehensive defense against a myriad of threats. In this blog, we will explore how digital security controls fortify our cyber defenses and ensure a safer digital environment for individuals and organizations alike.
Understanding Digital Security Controls
Digital security controls encompass a wide array of tools, processes, and technologies that collectively form a strong cybersecurity framework. These controls are designed to protect data, systems, networks, and devices from unauthorized access, data breaches, malware, and other cyber threats.
Bolstering Access Controls
Access controls are the first line of defense in cybersecurity. They govern who can access specific resources and ensure that only authorized users have the necessary permissions. Role-based access control (RBAC), least privilege, and multi-factor authentication (MFA) are some of the essential access control mechanisms that limit potential attack surfaces.
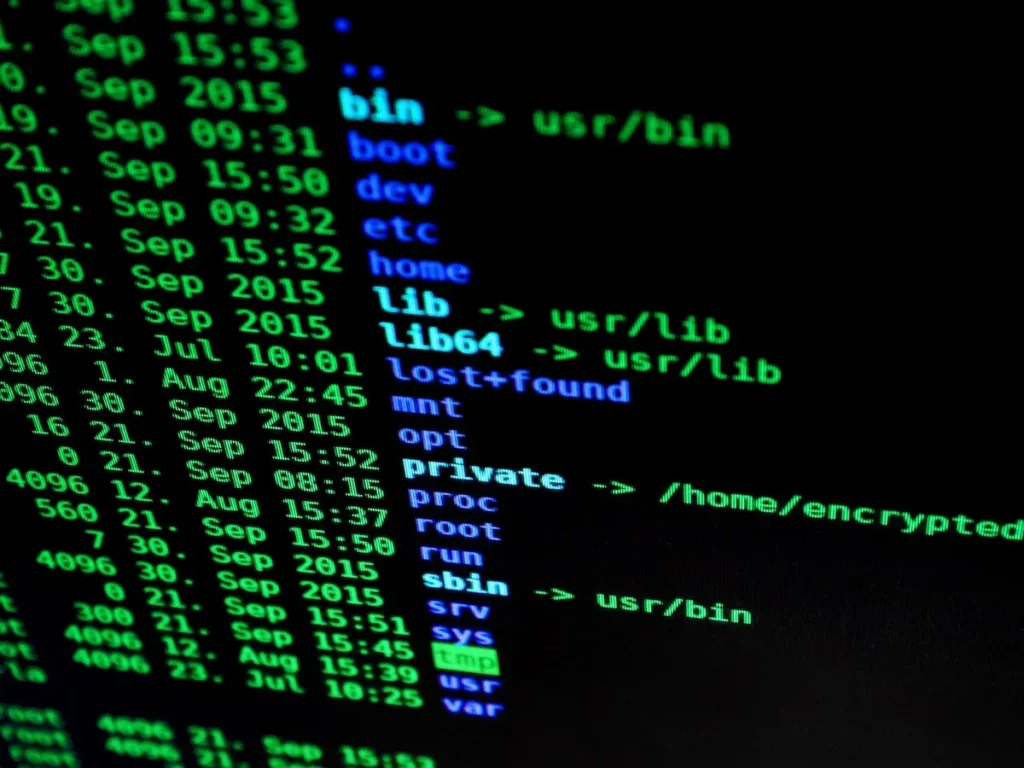
Safeguarding Data with Encryption
Data encryption is a critical aspect of digital security controls. By converting sensitive data into an unreadable format (ciphertext), encryption ensures that even if data is intercepted or stolen, it remains unintelligible to unauthorized parties. Robust encryption practices are instrumental in protecting data privacy and confidentiality.
Network Protection
Firewalls and Intrusion Detection Systems (IDS): Firewalls act as sentinels, monitoring and controlling network traffic to prevent unauthorized access and potential cyber threats. Intrusion Detection Systems (IDS) complement firewalls by detecting and alerting administrators to suspicious activities within the network. The combination of these digital security controls fortifies network protection.
Securing Endpoints
Endpoints, including laptops, mobile devices, and IoT devices, are often vulnerable points of entry for cyber attackers. Endpoint security solutions are designed to safeguard these devices from malware, ransomware, and other cyber threats. By ensuring the security of endpoints, organizations can strengthen their overall cybersecurity posture.
Incident Response and Preparedness
Despite comprehensive security measures, cyber incidents may still occur. An effective incident response plan is essential for timely detection, containment, and mitigation of threats. Incident response teams must be well-prepared to handle various scenarios and minimize the impact of cyberattacks.
Embracing Emerging Technologies
As cyber threats evolve, so must our digital security controls. Emerging technologies, such as artificial intelligence (AI) and machine learning (ML), are revolutionizing cybersecurity by providing real-time threat analysis, anomaly detection, and automated responses. Leveraging these technologies can enhance the efficiency and effectiveness of cybersecurity defenses.
Conclusion
In a world where cyber threats continue to evolve in complexity and sophistication, digital security controls have become the foundation of a robust cybersecurity strategy. By bolstering access controls, implementing data encryption, fortifying networks, securing endpoints, and preparing for incident response, individuals and organizations can enhance their cyber defenses significantly. Embracing emerging technologies further empowers cybersecurity professionals to stay ahead of evolving threats.
As we embrace the digital age, let us recognize the importance of digital security controls and their role in safeguarding our valuable data, privacy, and digital assets. By taking a proactive approach to cybersecurity and continually updating our defenses, we can create a safer digital ecosystem for everyone, ensuring that the benefits of technology can be fully enjoyed without compromising on security.



